Ethical hacking is the action of helping a third party to identify potential security vulnerabilities on your computer or network without compromising the integrity of the system or data. This activity has become extremely important to businesses, organizations, and other public or private networks because of the increasing sophistication of attackers and the willingness of many corporations to tolerate a small amount of risk in exchange for the assurance that their data will remain safe. In fact, the increased frequency of internet attacks has led many people to refer to the act of ethical hacking as ethical hacking. However, ethical hacking and ethical hackers are very different terms used to describe the same hacking conducted by an individual or company to help identify security vulnerabilities on a network or computer.
What Effects Can Ethical Hackers Have?
While it is not always clear what makes an ethical hacker, the answer generally falls into one of two categories. Some hackers are dedicated to breaking laws or regulations in the service of their country, and these types of attacks often have detrimental effects on legitimate systems. Other hackers may perform their attacks with the goal of sabotage. If an entity considers themselves to be conducting hacking activities for a political purpose, it is important to take action to stop them. While a number of countries prosecute political targets for sabotage, there are very few countries which actively monitor computer activity for political motives.
The most distinguishable characteristic between an authorized hacker and an unauthorized hacker is intent. While a hacker may view the target as a potential threat, they do so with the intention of stealing information to the benefit of the attacker. For example, the Anonymous group, which is well-known for posting DDoS attacks and other attacks against large corporations, does so with the intent of embarrassing large companies to remove their sites from the Internet. These groups may also use DDoS attacks in order to bring down a government website. While it is sometimes hard to differentiate hackers based on intent, there are a number of different types of hacking which fall into this category. While there are some common characteristics between different types of hacks (such as targeting an Internet service provider or a government agency), there are also subtle differences which make one hacking technique different from another.
Employed Techniques By Hackers
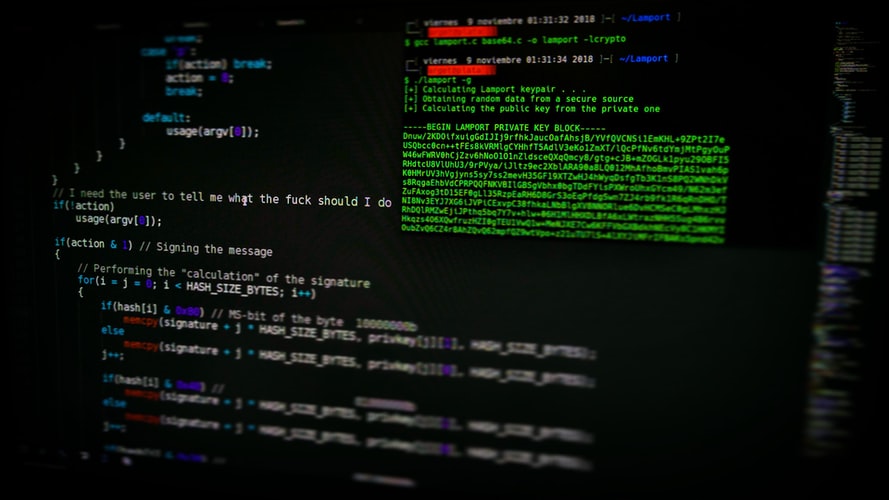
The most popular among ethical hacking techniques is “malware.” Malicious software is usually installed remotely, with the user unaware that it exists. This software can exploit a number of different types of vulnerabilities. The most commonly exploited software is adware, which is used to track the behaviour of users on the Internet and in online advertising networks.
Another type of ethical hacking technique is “fuzzing.” This technique involves testing an application’s functionality by exposing it to a range of different types of fake data, in order to determine whether the application crashes or operates inefficiently. In many cases, though, “fuzzing” requires a developer to intentionally expose a vulnerability in order to determine whether the program performs as expected. Many people think that fuzzing is only performed by programmers who write secure programs; however, there are some malicious attackers who use “side-channel” techniques in which they trick web developers into opening email attachments that contain viruses. If an ethical hacker can identify and execute this “bait” the consequences could be catastrophic.

Conclusion
There are many different types of ethical hacking techniques. When selecting a qualified professional for an ethical hacking job, it’s important to make sure that the individual has experience in all the different types of techniques that an experienced hacker may use. This way, if a vulnerability is discovered within an organization the right person can quickly address it. However, there are no guarantees that the selected professional has the skills necessary to exploit a vulnerability. A qualified professional should therefore have the skills and knowledge required to identify different types of threats and work to patch them accordingly.

Sophie Langford is passionate about cybersecurity innovations and securing online platforms against emerging vulnerabilities. Her expertise lies in implementing robust defense systems to safeguard businesses from evolving digital risks.